The sales landscape is rapidly changing with AI adoption. According to Gartner, 55% of sales organizations are already using AI,…
Read More
BLOG / NEWS
10 Ways To Avoid Losing Your Job To AI
CMG – June 19, 2025
The narrative that AI won't directly take your job is no longer comforting. AI is coming for your job directly,…
Read More
Bad Luck – Your CEO Doesn’t Think You’re as AI-Savvy as You Do
CMG – June 12, 2025
A Gartner report reveals a significant gap between CEO expectations and CIO capabilities. 77% of CEOs believe AI will define…
Read More
55% of CFOs Say Poor Cloud Network Performance Has ‘Stunted’ Operations
CMG – June 5, 2025
A recent survey found that finance chiefs are more frustrated than other executives with the performance of their cloud networks….
Read More
Enhancing Network Security Through Automated Configuration Management
CMG – May 29, 2025
In today’s rapidly changing digital environment, enterprise networks have grown increasingly complex, making security a top priority. Jaskirat Singh Chauhan,…
Read More
Interlock Ransomware Say It Stole 20TB of DaVita Healthcare Data
CMG – May 22, 2025
The Interlock ransomware group claims to have stolen 20TB of patient data from DaVita Healthcare, leaking 1.5TB and offering the…
Read More
Is This the Year of the Artificial Intelligence Call Center?
CMG – May 15, 2025
AI call center technology is transforming customer service by providing real-time feedback, predictive analytics, and in-depth analysis. This technology is…
Read More
How Do Automation and AI Impact Modern Cloud Operations?
CMG – May 8, 2025
The rise of cloud technology has transformed IT infrastructure management, with automation and artificial intelligence (AI) playing a key role…
Read More
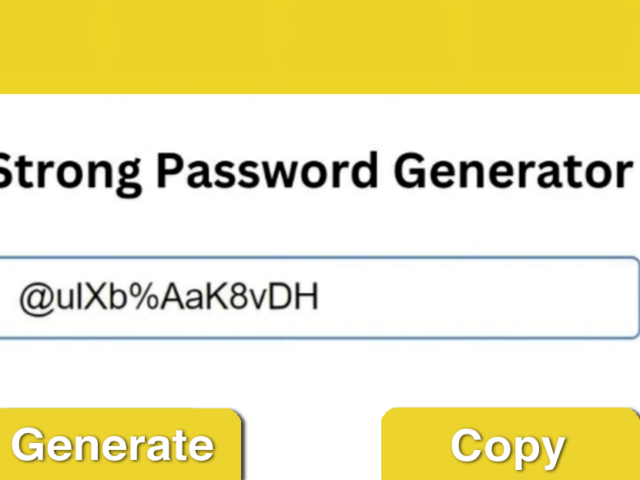
Is It Safe to Use Random Password Generators? Key Insights
CMG – April 24, 2025
A reputable random password generator is generally safe and offers strong protection against cyber threats. It creates complex passwords harder…
Read More
3 Ways Threat Intelligence Improves Business Security
CMG – April 10, 2025
Business security relies heavily on early detection and prevention of cyber threats. It's more cost-effective and beneficial for a company's…
Read More